 VeeMe Platform
VeeMe PlatformModular Document Intelligence
VeeMe Platform centralizes, secures, analyzes and automates your documents. Each module does one thing — and does it right.
Most organizations are drowning in documents
Documents everywhere
Critical information locked in PDFs, scattered across shared drives and email attachments.
Manual processes
People re-enter the same data, copy-paste between systems, waste hours finding files.
No traceability
Critical knowledge gets lost. No audit trail. No proof of who accessed what, when.
One platform. Five modules. Zero compromise.
VeeMe Platform is a modular architecture — deploy what you need, scale when you are ready.
VeeDoc — The document vault that cannot be compromised
Every document is envelope-encrypted with a unique key. Every action is logged in a tamper-proof chain. Every version is preserved forever.
Envelope Encryption
AES-256-GCM with per-document DEK wrapped by a master KEK. Zero-knowledge by design.
Hash-Chain Audit
Every action produces a cryptographically chained log entry. Tampering is mathematically detectable.
Immutable Versions
Every upload creates a new version. Soft-delete only. Nothing is ever truly erased.
Data Sovereignty
On-premise, private cloud, or hybrid. Your data never leaves your perimeter.
Everything you need to master your documents
Hybrid Search
Find information instantly — keyword and semantic search combined.
↗ Learn moreAutomatic OCR
Scanned documents become searchable text automatically.
↗ Learn moreSmart Summaries
Get the essential information from any document in seconds.
↗ Learn moreVersion Control
Every document version is preserved. Nothing is ever lost.
↗ Learn moreImmutable Audit Trail
Tamper-proof logs of every action. Prove compliance effortlessly.
↗ Learn moreEncrypted Storage
Data encrypted at rest and in transit. Your keys, your control.
↗ Learn moreHow VeeMe Platform works
From raw document to actionable intelligence — in three steps.
Ingest documents
Upload PDFs, Office files, images, scans. VeeDoc encrypts and stores them. VeeAI queues them for processing.
Analyze automatically
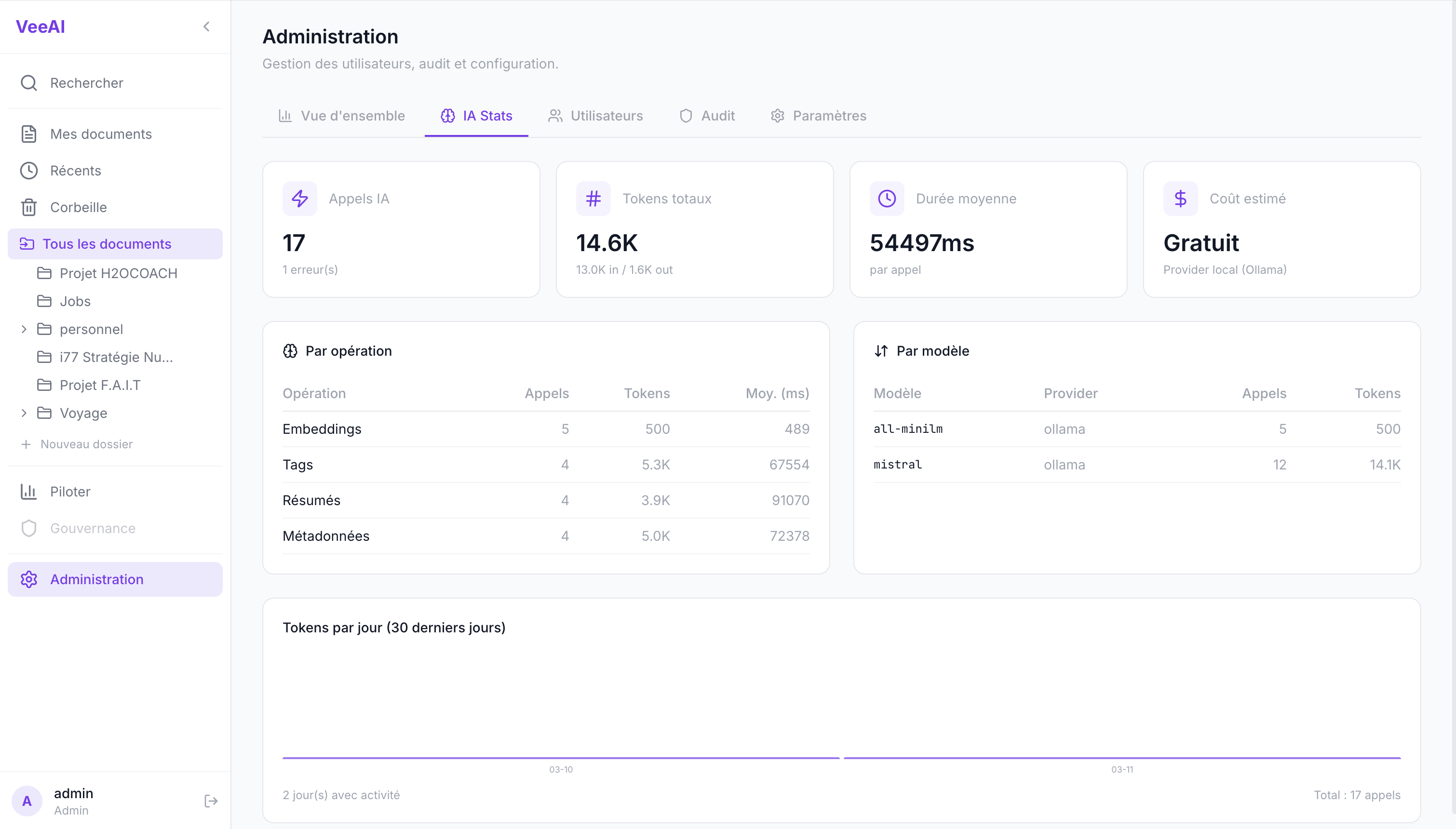
OCR extraction, metadata classification, AI summarization, vector embedding — all processed by async workers.
Search, automate, connect
Hybrid search finds anything instantly. VeeFlow triggers workflows. VeeConnect pushes to your systems.
Built for regulated industries
Contracts scattered across servers
VeeDoc vaults contracts. VeeAI finds related clauses by semantic similarity in seconds.
VeeDoc + VeeAI
Patient records compliance burden
Immutable encrypted storage meets HIPAA requirements. Hash-chain audit proves compliance.
VeeDoc + VeeFlow
Regulatory documentation chaos
Envelope encryption with audit chain. Automated workflows for document lifecycle.
VeeDoc + VeeFlow + VeeConnect
Data residency requirements
Full sovereignty — on-premise deployment, your keys, your infrastructure. No cloud dependency.
VeeCore + VeeDoc
Intellectual property at risk
Zero-knowledge vault with granular access control. Every access logged and hash-chained.
VeeDoc + VeeAI + VeeConnect
What is next
New modules in active development — extending the platform into collaboration, operations and field work.
VeeEdit
Collaborative document editing
Real-time co-editing with CRDT conflict resolution. Track changes, review cycles, and approval workflows — directly inside the vault.
VeeTerm
Terminal session documentation
Capture terminal sessions in real-time. Auto-generate runbooks, incident reports and change logs from actual commands. Built for sysadmins and DevOps.
VeeForm
Interactive forms and checklists
Build inspection forms, audit checklists and certification procedures. Conditional logic, offline support, photo capture. Designed for field teams.
We can't read your data. By design.
VeeMe Platform is built on a zero-knowledge, sovereignty-first architecture. You own your keys, your infrastructure, and your data.
Zero-knowledge
Per-document encryption keys. We mathematically cannot access your content.
Data sovereignty
Your data stays where you decide. On-premise, private cloud, or hybrid.
End-to-end encryption
AES-256-GCM envelope encryption. Compressed, encrypted, stored. You hold the master key.
Tamper-proof audit
Cryptographically chained logs. Every action traceable, nothing alterable.
Granular access control
Role-based permissions with relationship-based authorization (ReBAC). Enforced at every level.
Compliance-ready
GDPR, Loi 25, HIPAA. Built in, not bolted on.
Deploy the platform that respects your data
On-premise, private cloud, or hybrid. VeeMe Platform adapts to your infrastructure — not the other way around.