VeeDoc
Ultra-secure document vault
VeeDoc is a cryptographic document vault designed for regulated industries. Every document is encrypted with your local key — no one else holds it. Every action is recorded in a tamper-proof chain. Every version is preserved. Your data is mathematically inaccessible — even to us.
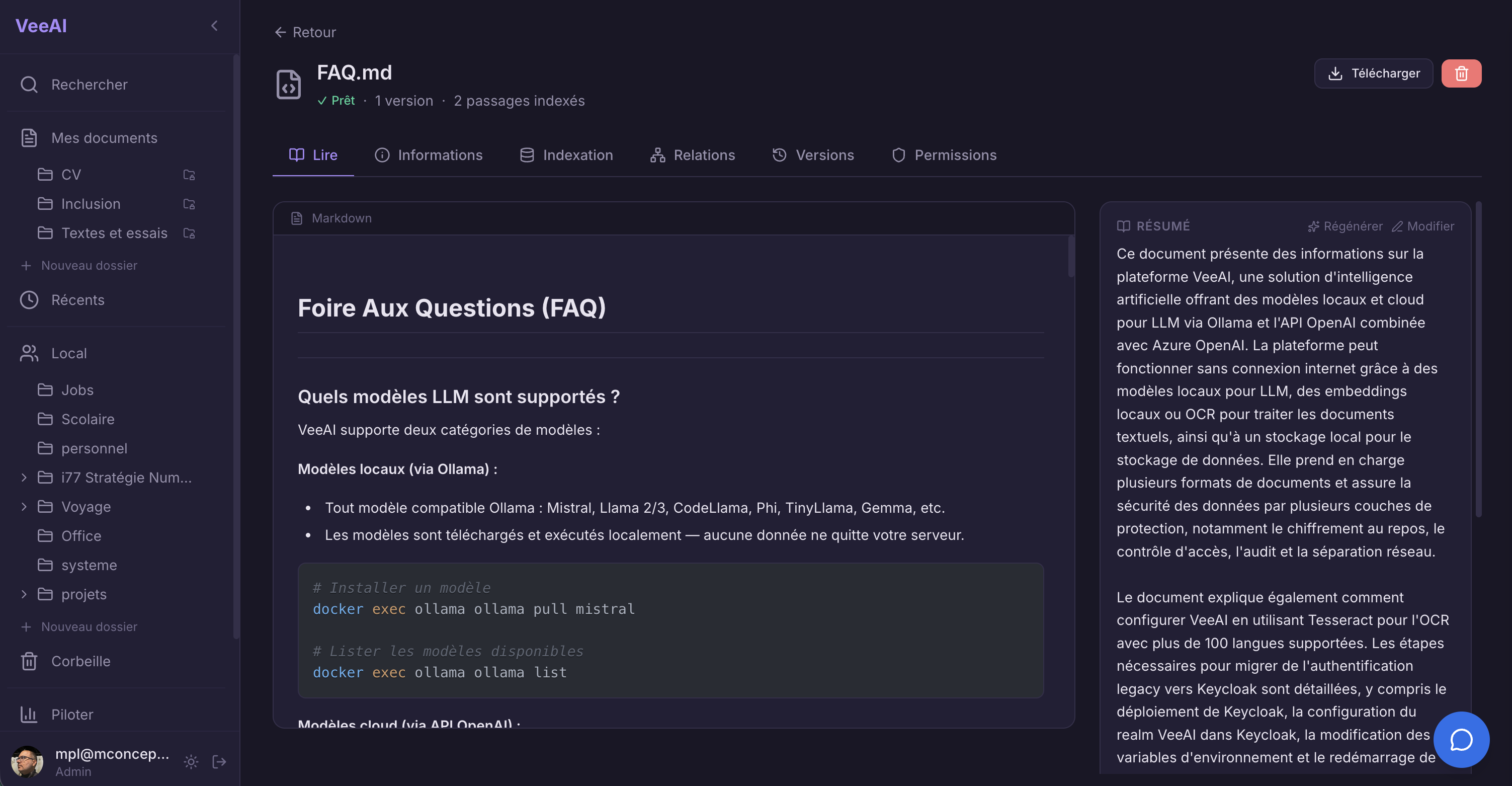
Architecture
Cryptographic Architecture
VeeDoc implements envelope encryption: each document gets a unique Data Encryption Key (DEK) generated at upload time. The DEK encrypts the document using AES-256-GCM. The DEK is then wrapped (encrypted) by a master Key Encryption Key (KEK) that you control. We never see the plaintext DEK — only the wrapped version. This is zero-knowledge by construction, not by policy.
Key Capabilities
VeeDoc
Envelope Encryption
Per-document AES-256-GCM encryption with unique DEK. Master KEK wraps all DEKs. Key rotation without re-encrypting documents. You hold the master key — zero-knowledge architecture.
Hash-Chain Audit Trail
Every action (upload, view, download, delete, share) generates an audit entry. Each entry includes a SHA-256 hash of the previous entry, forming a tamper-evident chain. Break one link, the whole chain invalidates.
Immutable Version Control
Every upload creates a new immutable version. Previous versions remain accessible. Soft-delete marks documents without physical erasure. Full document lifecycle tracking.
Relationship-Based Access Control
Authorization enforced via SpiceDB (Zanzibar-inspired ReBAC). Permissions are modeled as relationships: user to role to document. Checked on every API call, not just at the UI layer.
Compress-Then-Encrypt Pipeline
Documents are compressed (zstd) before encryption to maximize storage efficiency. Compression then encryption then storage. Decompression is transparent on retrieval.
Document Lifecycle Management
Configurable retention policies. Automated archival workflows. Legal hold support. GDPR right-to-erasure with cryptographic proof of deletion.